Consensus proofs consist of signatures from a supermajority subset of the entire validator set. This can result in the cost of verifying consensus proofs scaling linearly with the size of the validator set. However, the BLS signature scheme overcomes this limitation by enabling the aggregation of signatures and public keys, reducing verifier complexity to a single pairing check. Unfortunately, this comes at the cost of being unable to confirm the identity of each individual signer. The apk proofs[1] scheme reintroduces accountability in this regard at the extra cost of verification of a single SNARK proof.
The SNARK achieves this by constraining the elliptic curve addition of BLS public keys in order to produce a proof that a given aggregate public key is the result of the aggregation of a subset of a known set. You can see how this is useful for consensus proofs produced by a known validator set in POS consensus. This is done with the aid of half-cycles of elliptic curves. These half-cycles allow for embedding the field elements of an inner curve (which represents the public keys) within the scalar field of the outer curve. Where you can do polynomial commitments and opening proofs for the SNARK proof. Cycles of curves were first introduced for the purpose of recursive SNARK proof verification.
Preliminaries
I refer to the inner curve which is the native curve of the public keys as Einn. For an elliptic curve half-cycle, it should be the case that the characteristic of the base field of the inner curve Einn(Fp) is the same as the scalar field of the outer curve Eout(Fr). Let H be a suitably chosen multiplicative subgroup in the scalar field of the outer curve Eout(Fr).
APK Proofs
First we need to arithmetise elliptic curve point addition. Recall the elliptic curve addition formula P+Q=R for a short weierstrass curve, The slope λ between the two points is given as
λ=x2−x1y2−y1
Such that:
x3y3=λ2−x1−x2=λ(x1−x3)−y1
Substituting λ we get
x3=(x2−x1y2−y1)2−x1−x2x1+x2+x3=(x2−x1y2−y1)2(x1+x2+x3)(x2−x1)2−(y2−y1)2=0
In the same manner, we constrain the value for y3
y3=(x2−x1y2−y1)(x1−x3)−y1y1+y3=x2−x1y2−y1⋅(x1−x3)(y1+y3)(x2−x1)−(y2−y1)(x1−x3)=0
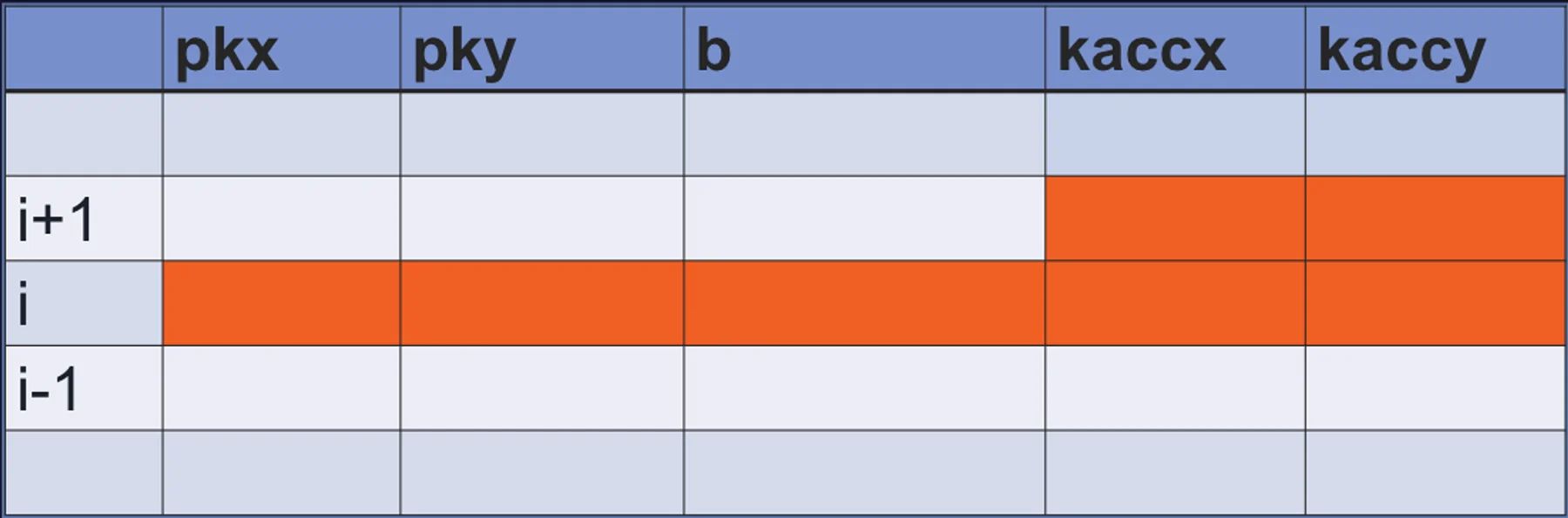
The goal is to show that apk=∑i=0n−1pki⋅bi, where pk is a vector of known public keys and b is a bitvector indicating the signers. We’ll do so by means of an accumulator. Observe that we can write
(kaccxi+1,kaccyi+1)=(kaccxi,kaccyi)⊕bi⋅(pkxi,pkyi)
Where pk{x,y} are the affine coordinates of the potential signers and kacc{x,y} is the accumulator sum.
Constraining with b we get:
b((y2−y1)2−(x1+x2+x3)(x2−x1)2)+(1−b)(y3−y1)=0b((y2−y1)(x1−x3)−(y1+y3)(x2−x1))+(1−b)(x3−x1)=0
Lifting these equations to polynomial constraints:
id1(X)id2(X)=(X−ωn−1)(b(X)((pky(X)−kaccy(X))2−(kaccx(X)+pkx(X)+kaccx(ω⋅X))(pkx(X)−kaccx(X))2)+(1−b(X))(kaccy(ω⋅X)−kaccy(X)))=(X−ωn−1)(b(X)((pky(X)−kaccy(X))(kaccx(X)−kaccx(ω⋅X))−(kaccy(X)+kaccy(ω⋅X))(pkx(X)−kaccx(X)))+(1−b(X))(kaccx(ω⋅X)−kaccx(X)))
Where
pkx(X)pky(X)kaccx(X)kaccy(X)b(X)=Li(X)⋅pkxi=Li(X)⋅pkyi=Li(X)⋅kaccxi=Li(X)⋅kaccyi=Li(X)⋅bi
Assume Li(X) are Lagrange polynomials in the domain H. The verifier has commitments to Cpkx and Cpky. They’ll receive the commitments and opening proofs for the polynomials, Ckaccx,Ckaccy and Cb. Which allows them to check the above polynomial constraints. Next we need to constrain the circuit inputs. We initialise the accumulator with a chosen point h∈Einn. Such that:
(kaccx0,kaccy0)=(hx,hy)(kaccxn−1,kaccyn−1)=(apkx,apky)⊕(hx,hy)
We’ll constrain using these equations.
(kaccx0−hx)+(kaccxn−1−(apkx+hx))=0(kaccy0−hy)+(kaccyn−1−(apky+hy))=0
Lifting to polynomial constraints
id3(X)=L0(X)(kaccx(X)−hx)+Ln−1(kaccx(X)−(apkx+hx))id4(X)=L0(X)(kaccy(X)−hy)+Ln−1(kaccy(X)−(apky+hy))
Finally the prover has to show that each bi∈{0,1}. They’ll do so using the polynomial constraint
id5(X)=b(X)(1−b(X))
In the Basic Accountable scheme, the bitvector is represented using individual field elements of the inner curve. This can be particularly expensive. In order to reduce space complexity of the bitlist and produce proofs of larger sets, it becomes necessary for the prover to represent the signers using the binary representation of each field element. This is more compact and saves significant communication complexity when dealing with signers of size 220 and above.
The paper introduces two new polynomials in it’s Packed Accountable Ranged scheme. First we must understand that any number z can be re-written as an inner product of its binary representation and powers of 2. This also known as binary decomposition.
z=⟨2i,zi⟩=i=0∑n−12i⋅zi
First we define block as the maximum number of bits in the binary representation in the field element we’ll use to represent chunks of our bitlist. The verifier can simply check that the pre-approved number of bits are used on in each of the field elements provided by the prover.
0≤countOnes(b′)<block
In order to use binary decomposition tricks, it’s necessary block is a power of 2. ie block=2k<n. Rather than a bitlist, the prover provides a vector of field elements b′
b′=(b0′,…,bblockn−1′)
where each bj′∈Einn(Fp) can be seen as
bj′=i=0∑block−12i⋅b(block⋅j)+i
The verifier wants to know that the bitlist encoded in the binary representation of b′ is equal to b(X). We do so by means of a range proof. Observe that
sum=j=0∑blockn−1bj′⋅rj=j=0∑blockn−1(i=0∑block−12i⋅b(block⋅j)+i)⋅rj=i=0∑n−12imodblock⋅bi⋅ri÷block
We begin by decomposing the final equation. First lets define a selector polynomial aux(X)
aux(X)=i=0∑n−1auxi⋅Li(X)
Where auxi is given as
auxi={10i∣blocki∤block
Note that 0 is divisible by any x. Next we define
ca(X)=i=0∑n−1ca,i⋅Li(X)
Where
ca,i=2imodblock⋅rblocki
The prover must then show that the following polynomial is zero over H
id6(X)=ca(ω⋅X)−ca(X)⋅(2+(2block−1r−2)⋅aux(ω⋅X))−(1−rblockn)⋅Ln−1(X)
Lets consider the case when i∤block, we have that:
id6(ωi)=ca(ω⋅ωi)−(ca(ωi)⋅2)=(2(imodblock)+1⋅rblocki)−((2imodblock⋅rblocki)⋅2)=rblocki(2(imodblock)+1−2(imodblock)+1)
Lets consider the second case when i∣block, we have that:
id6(ωi)=ca(ω⋅ωi)−ca(ωi)⋅(2+(2block−1r−2))⋅1=(20⋅r(blocki)+1)−(2block−1⋅rblocki)⋅(2block−1r)=r(blocki)+1−r(blocki)+1
Finally lets consider the case where i=n−1, It’s easy to see that ca,0=1. Therefore
id6(ωn−1)=1−(2block−1⋅rblockn−1)⋅(2+(2block−1r−2)⋅1)−(1−rblockn)⋅1=(1−rblockn−1⋅r)−(1−rblockn)=(1−rblockn)−(1−rblockn)
The polynomial id6(X) constrains the form of cai∈[0,(2imodblock⋅rblocki)]∀i∈[0,n−1). Next we introduce an accumulator polynomial for ca,i.
acca(X)=acca,i⋅Li(X)
where acca,i are the components of the vector:
[0,biti⋅ca,0,(bit0⋅ca,0)+(bit1⋅ca,1),…,i=0∑n−2(biti⋅ca,i)]
The prover must show that the following polynomial evaluates to zero over H
id7(X)=acca(ω⋅X)−acca(X)−(b(X)⋅ca(X))+sum⋅Ln−1(X)
Observe that
acca(ω⋅X)−acca(X)=biti⋅ca,i=b(X)⋅ca(X)
Therefore
id7(ωi)=(b(ωi)⋅ca(ωi))−(b(ωi)⋅ca(ωi))
Considering the case when i=n−1
id7(ωn−1)=0−(i=0∑n−2(biti⋅ca,i))−(b(ωn−1)⋅ca(ωn−1))+sum⋅1=−sum+sum
This convinces the verifier that b(X) is equivalent to b′. Finally the apk proof constraint polynomial t(X) is given as:
t(X)(Xn−1)=id1(X)(X−ωn−1)+α⋅id2(X)(X−ωn−1)+α2⋅id3(X)+α3⋅id4(X)+α4⋅id5(X)+α5⋅id6(X)+α6⋅id7(X)
Or in expanded form
t(X)(Xn−1)=(X−ωn−1)(b(X)((pky(X)−kaccy(X))2−(kaccx(X)+pkx(X)+kaccx(ω⋅X))(pkx(X)−kaccx(X))2)+(1−b(X))(kaccy(ω⋅X)−kaccy(X)))+α(X−ωn−1)⋅[b(X)((pky(X)−kaccy(X))(kaccx(X)−kaccx(ω⋅X))−(kaccy(X)+kaccy(ω⋅X))(pkx(X)−kaccx(X)))+(1−b(X))(kaccx(ω⋅X)−kaccx(X))]+α2⋅[L0(X)(kaccx(X)−hx)+Ln−1(kaccx(X)−(apkx+hx))]+α3⋅[L0(X)(kaccy(X)−hy)+Ln−1(kaccy(X)−(apky+hy))]+α4⋅[b(X)(1−b(X))]+α5⋅[ca(ω⋅X)−ca(X)⋅(2+(2block−1r−2)⋅aux(ω⋅X))−(1−rblockn)⋅Ln−1(X)]+α6⋅[acca(ω⋅X)−acca(X)−(b(X)⋅ca(X))+sum⋅Ln−1(X)]
Where α∈Eout(Fr) is a value chosen by the verifier. Given this constraint polynomial, it’s trivial to lift this further into SNARK using the PLONK protocol or any of it’s variants.
References
[1] Accountable Light Client Systems for PoS Blockchains, Oana Ciobotaru, Fatemeh Shirazi, Alistair Stewart, and Sergey Vasilyev.